Preventing cyber-attacks when they happen is less expensive than repairing the damage. Companies and organizations across industries lose money to cyber-attacks all the time. There are more apparent avenues, such as piracy, data breaches, and lawsuits.
Everything is digital these days, both on-premises and in the cloud. So cyber security personnel and security measures are something you will have to spend money on. But how should your company decide how much money to budget for security? And how should your company decide how to spend it?
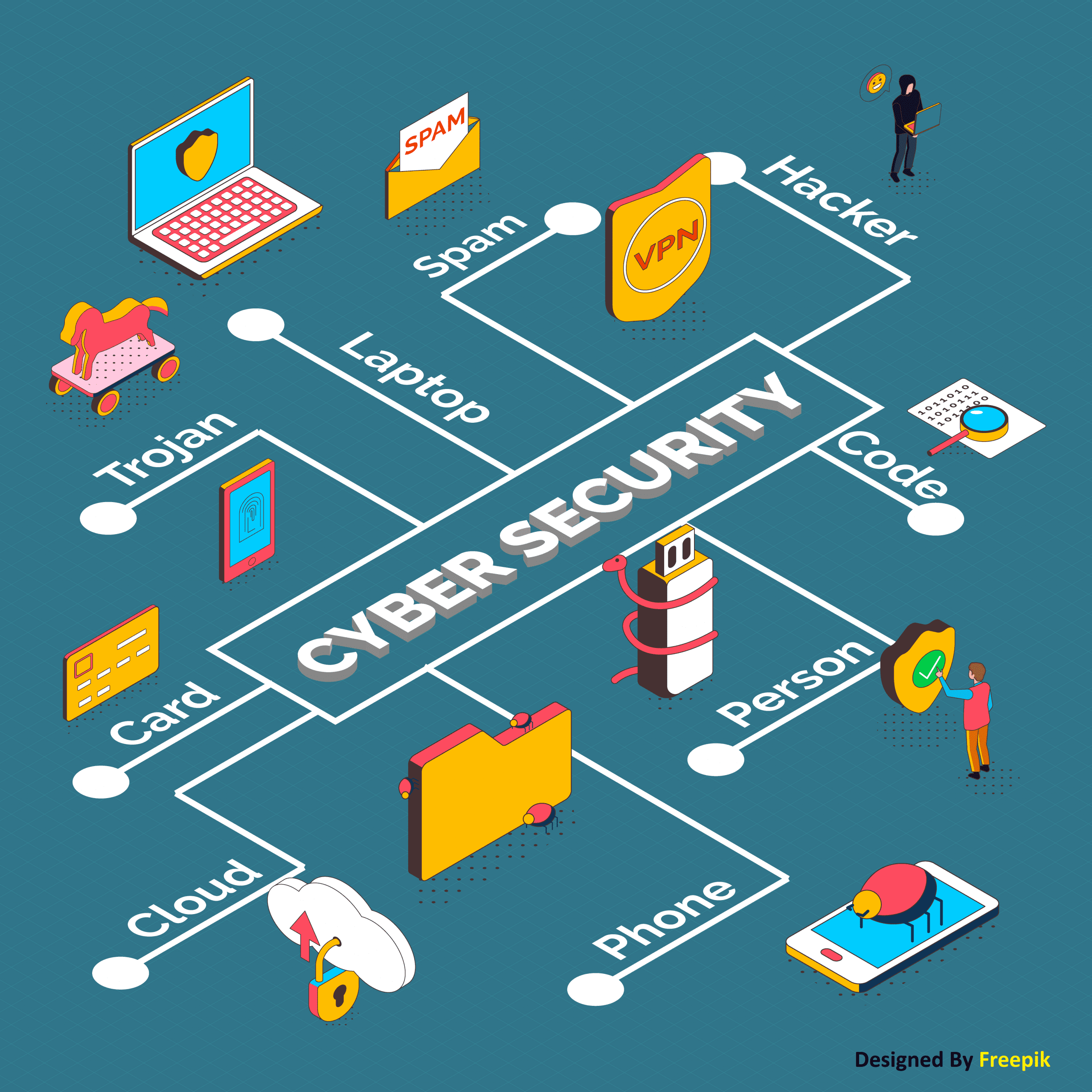
Creating a Cybersecurity Budget Breakdown:
All organizations should consider five main categories when allocating their cyber security maintenance contracts.
Compliance: Some compliance ordinances dictate security budgets distribute in the healthcare sector. For example, HIPAA defines data privacy and security obligation to protect individuals’ medical records and other personal health information. To meet these obligations and avoid potentially significant fines, CISOs must budget for specific tools and technologies.
Ongoing existing risk assessments: Proactive CISOs must continuously monitor the effectiveness of security controls in their environment and calibrate against prevailing attack vectors. Suppose the risk rises above a previously agreed-upon threshold. In that case, the CISO needs to assess the risk and discuss the risk with management to find another budget or reallocate the budget — or agree to accept a higher risk level. Tools and services for budgets in this category include cyber insurance, bug bounty initiatives, penetration testing, and incident response.
Ongoing security training: Security training is no longer an event on the annual mandatory compliance checklist. Every employee and contractor must be involved in this ongoing effort. Using public shame or fear to motivate employees is not adequate. Instead, cybersecurity training needs to be memorable.
New business initiatives: A CISO must evaluate any new business initiative adopted within the company and implement a security budget to ensure that the company and its new customers remain secure. For example, marketing departments may outsource content creation to an overseas third-party provider or decide to store all customer support cases in a cloud storage platform. Both of these scenarios have additional risks, which CISOs and security teams should address before implementing.
Business priority shifts: It can be related to people, technology, or revenue. From a public perspective, an example of a business priority shift is the hybrid, or, in some cases, permanent work-from-home model and the adaptation required to maintain cybersecurity best practices. From employee onboarding — and offboarding — to employee use of a shared home router, local offline data storage, home privacy needs to personal devices, and video conferencing, all require security adaptation and budget realignment.
What is a typical cybersecurity budget?
While there is no versatile answer when determining what a “typical budget” looks like for cybersecurity operations, some studies can provide some sensitivity.
Recent research by Deloitte and the Financial Services Information Sharing and Analysis Centre found that financial services spend an average of 10% of their IT budgets on cybersecurity. It costs approximately 0.2% to 0.9% of company revenue or $1,300 to $3,000 per full-time employee. For a more significant picture specification, consider that Microsoft CEO Satya Nadella recently disclosed in a statement that the tech behemoth would “invest more than $1 billion annually in cybersecurity for the foreseeable future”. Finally, it is worth noting that the US President’s 2019 budget allocated $15 billion to spend on cybersecurity, which is about 0.3% of the entire economic budget ($4.746 trillion).
Resource:
https://www.mstech.com/client-contract-includes-cybersecurity-restrictions/
https://www.techtarget.com/searchsecurity/tip/Cybersecurity-budget-breakdown-and-best-practices
https://cybersecurity.att.com/blogs/security-essentials/how-to-justify-your-cybersecurity-budget
Disclaimer:
Wherever any material is quoted as sourced from the published text with publishing rights vested in an individual, it is stated that it is a pure quotation and has no intention to claim it as our own.
Image Source: www.freepik.com