The amount of data being stored by businesses contains a range of information, from buying trends to customer’s data. As a result, every company in possession of confidential or sensitive information is looking for proven ways to protect their data assets. With more and more businesses operating digitally, the exposure to potential risk increases.
Considering that hacks are on the rise, and security incidents are not uncommon, it’s important that your company continues to explore methods to shield your customer’s data from malicious actors. Here are four tips when it comes to protecting your customer’s data.
1. Choose the Right Tools
Businesses are collaborating and sharing information with team members, vendors, and various partners on a daily basis. This is a necessity for businesses with remote staff members, which have increased since the onset of the COVID-19 pandemic.
In order to safeguard against this as a security flaw, companies must choose collaboration and communication tools that are secure. When choosing a cloud storage provider or deploying project management tools, companies should be prioritizing security.
Any digital tool that allows employees or clients to access documents or request information from databases should be analyzed for potential risk. A major component here is also the training around these tools. When team members understand the technology you’re using, the company as a whole is better protected.
2. Replacing FTP Scripts
There are many organizations that are still exchanging information using custom programs or scripts. Being that this methodology is now considered outdated, this process presents a security risk.
The architecture of FTP scripts is typically very vulnerable, and offers limited control of data. As a result, they are not accepted by the primary compliance regulations, and their use should be stopped immediately. As a replacement, consider secure FTP solutions that guarantee confidentiality. Using an alternative will improve security while providing total control and traceability of data movements, which ensures compliance with regulations.
3. Locate Compromised Devices
The prowess of modern hackers should not be overlooked, which is why any device with an internet connection should be considered “at risk”. Whether it is a work computer, personal smartphone, or even a connected smart device, hackers are looking to exploit the technology to acquire valuable data from businesses and their customers.
Businesses must remain proactive, and work to locate any compromised devices in your internal network. Additionally, it is important to consider the deployment of solutions that focus on network traffic inspection and threat detection. There are a number of options on the market available, and they provide advice on what is needed in order to avoid the threat of a data breach.
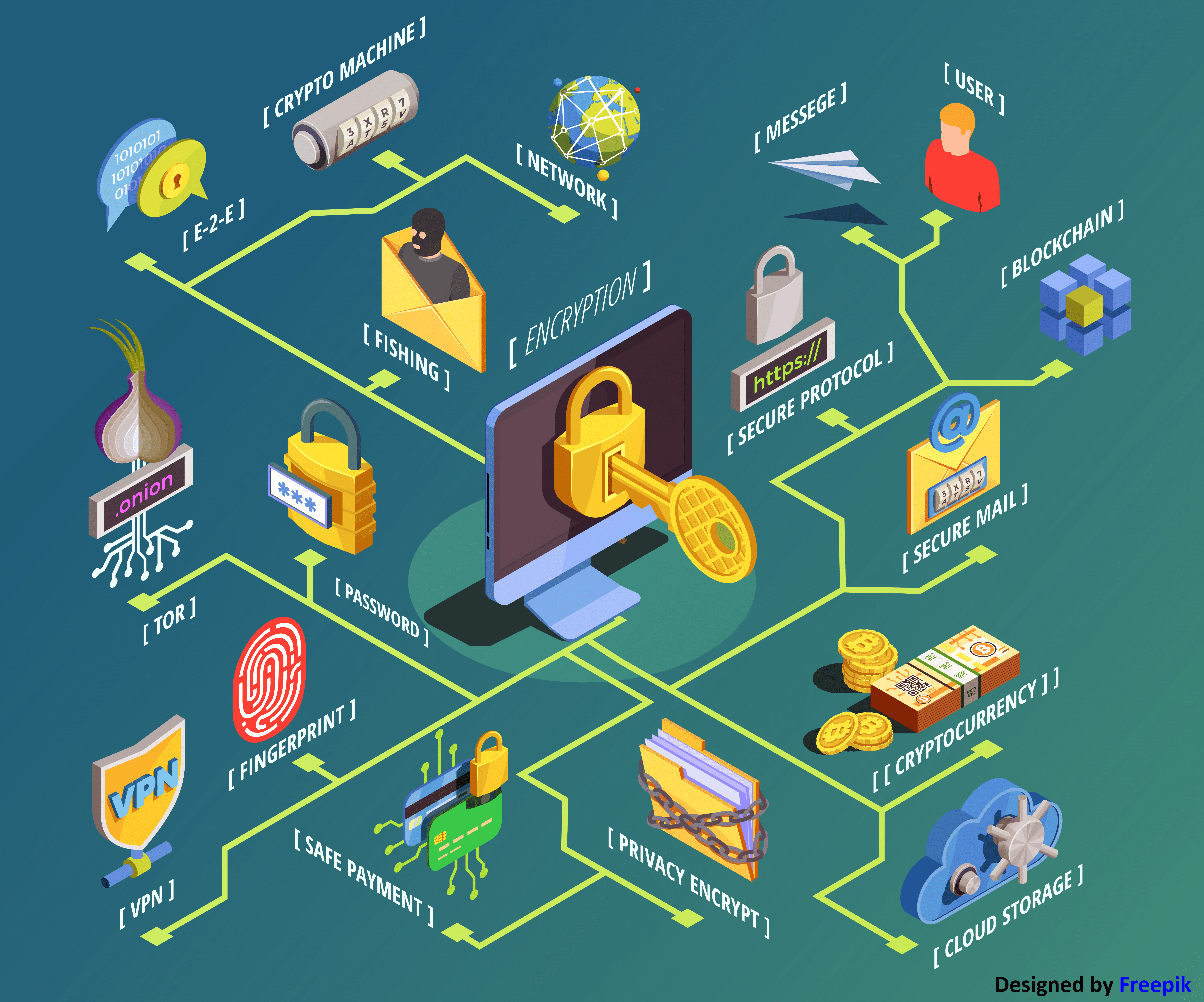
4. Data Encryption
Data that is being stored or shared should always be encrypted, as this ensures its confidentiality. The major benefit being that encrypted data is unreadable should it be accessed by someone without permission. This is why data encryption is so powerful.
File transfer software encrypts data in transit, and rights management solutions help control access to documents and information, despite the location of the data. There are a number of options available when it comes to encryption software. Always make a decision based on your specific needs and the desired outcome.
Disclaimer:
Wherever any material is quoted as sourced from the published text with publishing rights vested in an individual, it is stated that it is a pure quotation and no intention to claim it as our own.
We suggest that businesses look at their vulnerabilities and constantly work to improve their data protection. Avion Technology specializes in assisting throughout this search for improved data security solutions. To learn more about our unique approach to programming, click here
Image Source: www.freepik.com