Small businesses are just as vulnerable to cyber security threats as large enterprises. A common misapprehension for small businesses is the idea of safety by unimportance that your business is too small-scale to be a target, but regrettably, that’s not the case.
As attackers automate more and more attacks, it’s easier for them to target hundreds, if not thousands, of small businesses at once. Small businesses often have less stringent technical defenses, less consciousness of threats, and less time and resources for cyber security. It makes them easy targets for hackers than larger businesses.
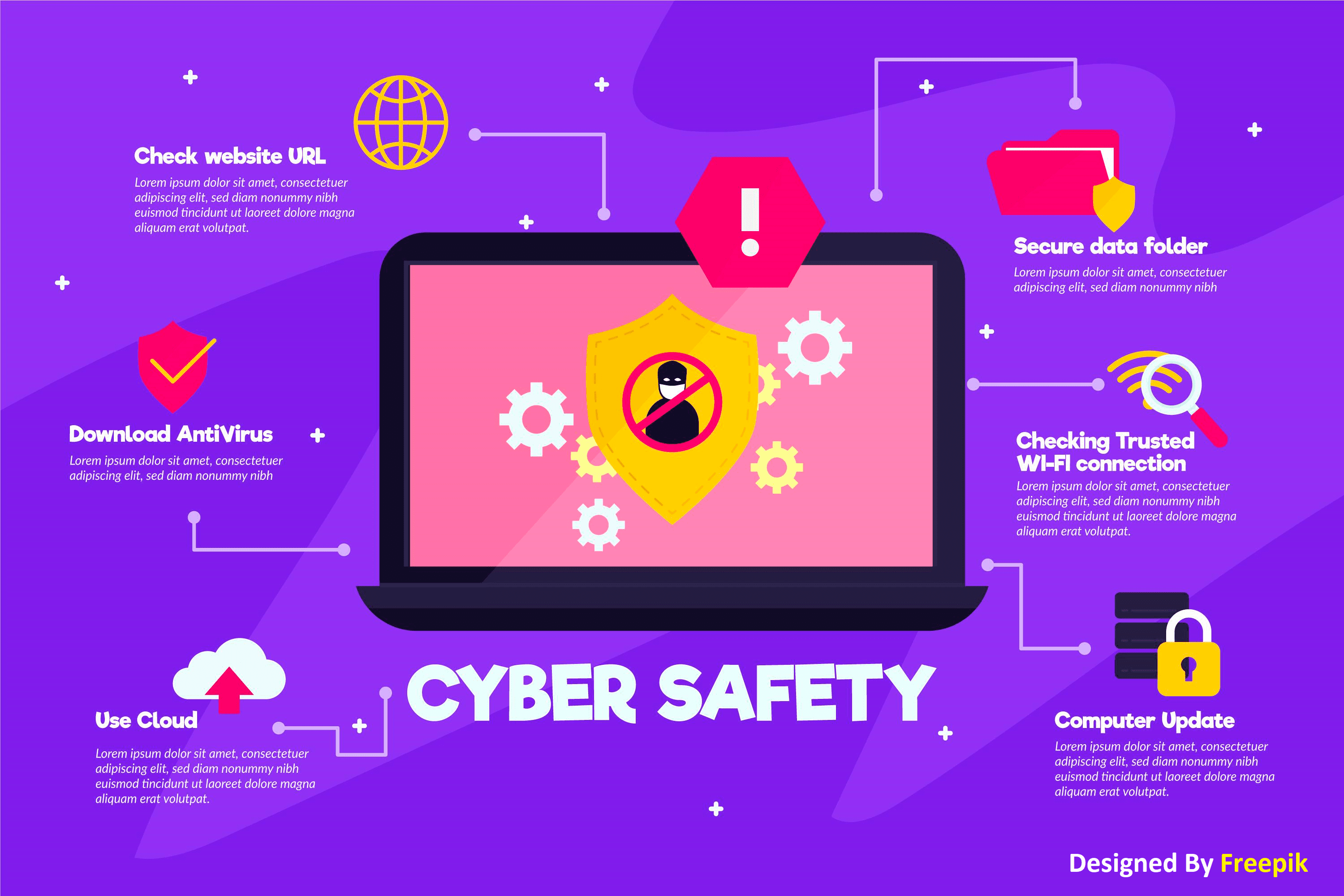
For these reasons, agency clients need to be aware of threats and how to stop them. This article will cover the Top 5 cyber threats you need to make your agency clients aware of.
Phishing Attacks: Phishing is one of the most prominent and widespread types of cyber-attacks. The social engineering attack is where the attacker impersonates a trusted contact and sends fake mail to the victim. The victim opens the mail and clicks on the malicious link or opens the attachment of the mail. Phishing attackers gain access to confidential information and account credentials by doing so.
Malware Attack: It is one of the most common cyber-attacks. “Malware” refers to malicious software viruses, including worms, spyware, ransomware, adware, and Trojans. A Trojan virus disguises itself as legitimate software. Ransomware blocks access to critical components of a network, while spyware is software that steals all your confidential data without your knowledge. Malware breaches networks through vulnerabilities. When a user clicks on a dangerous link, downloads an email attachment, or when a contaminated pen drive is used.
Weak Passwords: Another significant threat small businesses face is employees using weak or easily guessed passwords. Many Agencies Clients use multiple cloud-based services, which require different accounts. These cloud-based services can often contain sensitive data and financial records. Using easily guessed passwords, or using the same password for multiple accounts, can compromise or hack this data.
Man in the Middle: A man-in-the-middle attack is also known as an eavesdropping attack. In this attack, the attacker comes in between the two-party communication, i.e., hijacks the session between the client and the host. By doing this, hackers steal and manipulate your data. The client-server communication is cut off; the communication line goes through the hacker.
Denial-of-Service Attack: Denial of service is a significant risk for companies. In this attack, Attackers target systems, networks, or servers and flood them with traffic to exhaust their resources and bandwidth. When this happens, it becomes overwhelming for the server to keep up with incoming requests, resulting in the website it hosts either shutting down or slowing down. The leaves legal service requests need to be addressed. It is also known as a DDoS attack when attackers use multiple compromised systems to launch this Denial-of-Service attack.
Resource:
https://expertinsights.com/insights/the-top-5-biggest-cyber-security-threats-that-small-businesses-face-and-how-to-stop-them/
https://onlinedegrees.und.edu/blog/types-of-cyber-security-threats/
https://www.simplilearn.com/tutorials/cyber-security-tutorial/types-of-cyber-attacks
Disclaimer:
Wherever any material is quoted as sourced from the published text with publishing rights vested in an individual, it is stated that it is a pure quotation and has no intention to claim it as our own.
Image Source: www.freepik.com